“SIMPLE DUE DILIGENCE”
by Sharon Rondeau

(Sep. 2, 2019) — That the U.S. government is conducting surveillance on its citizens is now indisputable given former CIA contractor Edward Snowden’s revelations made to The Guardian and published June 6, 2013. Days later, then-Director of National Intelligence James Clapper was forced to admit that his previous statement to the Senate Intelligence Committee just three months earlier that surveillance was not “wittingly” occurring on Americans was inaccurate.
In December 2013, Freedom Watch and Judicial Watch founder Larry Klayman won a landmark case in which U.S. District Court Judge Richard J. Leon ruled that the NSA’s bulk collection of Americans’ communications was “likely unconstitutional.” In late May 2015, Congress allowed provisions of the Patriot Act associated with surveillance to expire and shortly afterward, passed the USA Freedom Act, which eliminated the Patriot Act’s controversial Section 215.
At 2:23 in an August 4 interview initially focusing on government surveillance, former NSA program developer J. Kirk Wiebe told host Sarah Westall that he and fellow former NSA colleagues William Binney and Thomas Drake analyzed “65 hard drives” delivered to them by “two detectives” who he identified as “Mike Zullo” and “Brian Mackiewicz.”
As Zullo has detailed, he and Mackiewicz were authorized by the Maricopa County Sheriff’s Office (MCSO) to obtain an analysis of “approximately 45 high-capacity external computer drives” supplied by former NSA and CIA contractor Dennis Montgomery to the MCSO said to contain highly-classified information demonstrating warrantless government surveillance on millions of Americans and specifically, residents of Maricopa County.
After providing some evidence on thumb drives which Zullo found to be “creditable” and “verifiable,” then-Maricopa County Sheriff Joseph Arpaio hired Montgomery to work as a confidential informant for approximately a year. Montgomery’s work consisted of transferring the evidence he claimed to have onto hard drives purchased by the Sheriff’s Office at a salary, Zullo said, of $10,000 monthly.
On Friday, Zullo told The Post & Email exclusively that after approximately two months, he became suspicious of Montgomery’s claims and suspected that the hard drives did not contain the highly-sensitive information and evidence Montgomery had promised, prompting him to make those concerns known to the Sheriff’s Office officials and to seek an expert opinion in Binney, Wiebe and Drake some months later.
Zullo met with the three former NSA employees on two occasions, he told The Post & Email, and included for analysis the six thumb drives which Zullo said contained the “verifiable” information.
In an email dated November 14, 2014 from Drake to Mackiewicz with an attached analysis report, Drake and Wiebe wrote that they found the data on the hard drives to lack sourcing and to be “a whole lot of faked and made up documents and analysis.”
On page 1 of the report, speaking of themselves in the third person, Drake and Wiebe wrote that they identified “non-conventional coding formats and classification caveats not resembling typical government practice.” Further, they said, “the three code files were actually fake and framed to look like real code but crudely cut and pasted from snippets of existing code” and that other material in the form of “comments” “were clearly and simply manufactured to make them look real.”

Zullo said he recalls the number of hard drives he gave to the three as “47,” while Wiebe told Westall he and Drake analyzed “65” hard drives. The report says they analyzed “approximately 45” drives. At 3:20 in the Westall interview, Wiebe said the number was “64.”
As opposed to his findings of nearly five years ago, Wiebe contended to Westall that Montgomery, who had a security clearance at one time, would have known that by law he could not place classified information on the drives and provide them to individuals not authorized to see it. At 6:10, however, he suggested that while he and Drake found “nothing of intelligence value” on the drives, Montgomery could have been providing a “hint” that he had useful information stored elsewhere.
Zullo told The Post & Email that when initially meeting with the three, he suggested the same to Wiebe, Drake and Binney. However, Montgomery continued to maintain he had placed Top Secret information on all the drives which was later discovered to be untrue.
At the time Zullo met with Drake, Binney and Wiebe, Montgomery had not yet approached the FBI with the information he said he had as evidence of illegal government surveillance, although that would occur twice in the latter half of 2015, arranged by Klayman.
At 7:54, Wiebe told Westall that Zullo and Mackiewicz did not inform them that in 2007, then-DNI John Negroponte had invoked the State Secrets Privilege on Montgomery in a civil case filed by Montgomery against the company he had formed with Warren Trepp, eTreppid Technologies, LLC. Wiebe also claimed that when Montgomery testified to Judge Lamberth, Lamberth placed a “gag order” on Montgomery, a claim with which Zullo, who was present during the meeting, disagrees.
Zullo additionally has said he and Mackiewicz informed Binney, Drake and Wiebe that Montgomery had been read into a “Special Access Program,” or “SAP,” and that Montgomery was the subject of a State Secrets Privilege invocation on one occasion back in 2007.
At 8:29, Wiebe told Westall, “It now makes sense why Dennis did what he did.”
Westall and her colleague, Dr. Dave Janda, as well as Fanning and Jones, have tied the late Adm. James “Ace” Lyons to specific knowledge of The Hammer and its capabilities. Although former CIA Director John Brennan has been connected to the use of the technology in 2009, he was not then serving in that capacity.
At 9:06 in the interview, Westall struggled to recall Lyons’s name and rank prior to his passing late last year but placed his name in the caption to the video interview with Wiebe.
“He may know something we don’t,” Wiebe responded, as if Lyons were still among the living.
At 14:02 in the interview, Wiebe decried the fact that government entities are using “parallel construction” methods to obtain information on Americans without a warrant and failing to divulge the source of the information to criminal defense attorneys, for example. At 18:04, Wiebe contended, “This threatens our way of life.”
An FBI “302,” or interview summary, included in Trepp’s 2006 civil suit against Montgomery, depicts Trepp’s statements made to “Special Agents John Piser III and Michael A. West” (begins on p. 3) in Reno, NV on January 31, 2006.
The Air Force had a contract with eTreppid to develop “data compression and pattern recognition” software at the time Montgomery left the company in January 2006, with additional contractual work expected, Trepp told FBI agents. Trepp sued Montgomery in Nevada state court for allegedly taking the company’s source codes, after which Montgomery sued Trepp in federal court.
As The Post & Email has reported, eTreppid’s work for the Air Force became the subject of an invocation of the State Secrets Privilege and a protective order in 2007, which Montgomery claims to still be in effect and which Fanning and Jones have repeated. However, due diligence reveals that in the case of United States v. Reynolds, the State Secrets Privilege applies on a case-by-case basis and can be invoked only by a government agent.
Page “3” of the FBI 302 documenting agents’ interview of Warren Trepp states that Trepp informed them on January 31, 2006:

The FBI additionally noted:

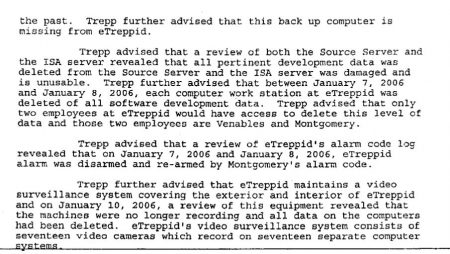
On pages “4” and “5” of the 302, respectively, the FBI wrote:



The complete 302 can be accessed here: 275559455-DM-FBI-Search-70-Gov-Docs-Unsealed-D-nev-3-06-Cv-00263
An excerpt from page 101 of an interview between an eTreppid employee and the Air Force Office of Special Investigations reads:
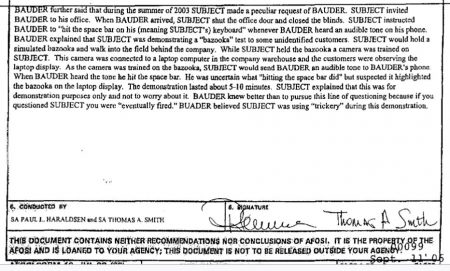
A second account from another employee relates the same scheme (p. 100).
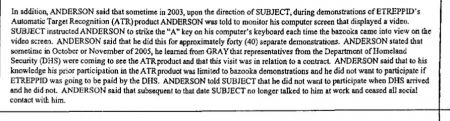
On page 93, Air Force Office of Special Investigations Special Agent Paul L. Haraldsen reported that Trepp said that “backup copies” of the source code used by eTreppid which Montgomery “was required to provide on an annual basis” were discovered to be “worthless and did not contain the data SUBJECT was required to provide.”

It should be noted that this was the same discovery made by Zullo on the 47 hard drives Montgomery supplied to the Sheriff’s Office, confirming Zullo’s earlier suspicions.
A report by Haraldsen dated February 14, 2006 states that “The Theft of the intellectual property prohibited the U.S. Government from awarding eTreppid Technologies a contract to develop technologies to be used for prosecuting the Global War on Terrorism” (p. 108)

Beginning at page 108 in the transcript of a “Show Cause” hearing in Montgomery v. eTreppid, under questioning by the defendant’s attorney, Montgomery contradicted his previous testimony and declared (p. 110), “I don’t know if classified information and the State Secrets Privilege, and the protective order are all the same thing.”


According to an article in Mother Jones dated August 30, 2007 (internal links are now dysfunctional), “The FBI is reportedly investigating Nevada governor Jim Gibbons, a former Congressman and House Intelligence committee member, for possible corruption. The crux of the corruption probe centers on alleged evidence that Gibbons accepted trips, gifts and cash from a Nevada defense contractor, Warren Trepp, of eTreppid, in exchange for throwing eTreppid defense and intelligence contracts – many of them apparently from the black budget. Trepp, in turn, has enlisted the help of the FBI, in going after a former employee, Dennis Montgomery, who provided his firm key technology and took it with him when he left the company. There’s been lots of spooky stuff about the legal process playing out between Montgomery and Trepp, with an Air Force special investigator apparently having enlisted the FBI to help Trepp go after Montgomery, the sealing of documents, and other mysteries suggesting the Air Force really really doesn’t want a court process to uncover just what it hired eTreppid to do.”
The following year, the FBI cleared Gibbons of any wrongdoing of which Montgomery accused him. On November 2, 2008, Matt Apuzzo, then of the AP and now of The New York Times, reported Gibbons as having said, “Two years ago when this story broke I told my side of it, that I had nothing to do with it. Today I am exceedingly pleased that the FBI and the Justice Department have vindicated me from the allegations and claims of Mr. Montgomery.”
During discovery in the case, Montgomery was accused of fabricating emails allegedly belonging to Gibbons. Zullo also stated that fabricated emails were discovered on the 47 hard drives Montgomery turned over to the Sheriff’s Office.
On September 23, 2008, Businesswire reported that eTreppid Technologies and Montgomery, who had formed another software company, Blxware, with financial support from Edra Blixseth, had reached a confidential settlement agreement.
In 2009, Edra Blixseth filed for Chapter 7 bankruptcy and liquidated the company.
It was Tim Blixseth, Edra’s ex-husband, who first approached the MCSO in 2012 to relate Montgomery’s claims of massive data-harvesting by the U.S. government, including on 151,000 Maricopa County residents. While Fanning and Jones have touted the recordings Zullo made of the encounters among Tim Blixseth, Montgomery, Mackiewicz, Arpaio, and himself as “The Whistleblower Tapes,” none of the claims has ever been conclusively proven.
The recordings were not “found” by Fanning and Jones, but rather, leaked to The Phoenix New Times by ACLU plaintiffs’ attorney Cecillia Wang in early November 2015 by her own admission, without the court’s prior approval.
In response to the FBI and AFOSI findings relating to Montgomery, Zullo said:
All the Fanning interviews are designed for one purpose and one purpose only: to whitewash Montgomery and give him the appearance of credibility. However, the facts are the facts, and history absolutely repeats itself as far as he is concerned.
Looking to all the evidence in Montgomery’s prior legal entanglements, he has repeatedly been characterized as a “liar,” “conman,” as “vindictive,” an embellisher of stories and his abilities when it suits him to do so. The list goes on and on.
Let me explain the negative impact of our investigative dealings with Montgomery and put it all in perspective and you will understand why Fanning does Montgomery’s bidding and attempts to create distance for Montgomery from the Sheriff’s Office investigation.
Montgomery frauded the Sheriff’s Office concerning the “47” hard drives. I am not a lawyer, but let me try to give you an understanding of the anatomy of a fraud.
Let’s start with the elements of fraud. A fraud has a very specific set of elements that need to be met in order for a criminal violation to have occurred.
- Misrepresentation of material facts.
- The perpetrator with full knowledge is aware they are misrepresenting the facts.
- The misrepresentation was purposeful and with the intent to deceive the victim.
- The victim ultimately believed and relied and acted on those misrepresentations.
- The victim suffered damages as a result.
So in Montgomery’s case his interaction meets all of these elements of a fraud.
- Montgomery represented that he had Classified Secret Government Digital Information of a criminal nature retrieved while he was a contractor working for the CIA and wanted to become a whistleblower and turn this evidence over to Law Enforcement. He maintained the information was illegally and surreptitiously obtained by unauthorized government programs and personal confidential information was gathered on the unsuspecting public and constitutional rights had been violated. He agreed to place that digital information on 47 hard drives and turn them over to investigators as evidence of his claim, with the caveat that only those with appropriate governmental clearance could view the drives’ content (1. Misrepresentation of material facts).
- Montgomery has full knowledge that he had no intention of fulfilling these representations and had no intention of putting classified evidence on those specific hard drives. This is evidenced later on after examination. (2. The perpetrator with full knowledge is aware they are misrepresenting the facts).
- Montgomery created some 47 hard drives over time, one at a time, and handed them over to investigators, again making the very same representation, over many months, that Top Secret Classified information was contained on them. This representation proved to be entirely false (3. The misrepresentation was purposeful and with the intent to deceive the victim).
- Based on limited, separate, initial credible information provided to investigators by Montgomery, along with the fact that he was in possession of the identities of 151,000 residents of Maricopa County, investigators relied on Montgomery’s representation and agreed to participate (4. The victim ultimately believed and relied and acted on those misrepresentations).
- Montgomery was compensated thousands of dollars for creating the hard drives, but all the while Montgomery, by his own hand, created and turned over nothing but digital garbage to investigators some 47 times over. 47 worthless hard drives he created, as he continued to represent each of them as containing highly classified information, so much so that Montgomery was cautioning investigators not to look at the data due to the fact there was classified information contained and would require a specific government security clearance to do so.
- Subsequently, investigators discovered there was not one shred of classified information or anything of value whatsoever on those 47 hard drives that he was compensated to produce. Montgomery frauded the Sheriff’s Office for compensation and other expenses as a result of his fraudulent representations and perpetual scheme (5. Victim suffered damages as a result).
So did this really happen? You bet it did. And you have to look no further than Mary Fanning, who totally admits the con publicly as she attempts to justify Montgomery’s fraudulent actions with a straight face. Courtroom testimony by all witness for the Sheriff’s Office have testified to the same event. Some simple due diligence on Fanning’s part would have shed light on Montgomery.
Who is the perpetrator? Montgomery. Who is the Victim? The Sheriff’s Office. How was the victim damaged? Monetarily.
Montgomery wants to pretend this never happened and Fanning and Jones are all too happy to accommodate and offer up a contrived narrative.
Now as we turn to Montgomery’s history, it will be clear for all to see that this is not the first time Montgomery demonstrated this type of brazenly deceptive ability.
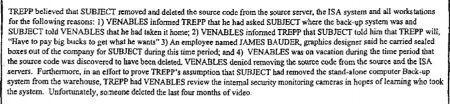
The FBI 302 contains a number of firsthand accounts of those who worked with Montgomery at eTreppid. Some of the observations were not only reported to the FBI but the Air Force Office of Special Investigations as well.
Some of the observations include firsthand accounts of Montgomery’s deceptive schemes as told to federal investigators by those innocently involved to include an attempt to defraud the government and dupe them into purchasing inoperable software that Montgomery claimed he developed. Also other employees believed Montgomery did not possess the skills required to write software code to the level expected in his position. Employees believed that Montgomery sabotaged his employer, including deletion of source code and the removal of hard drives from his employer.
And the list goes on.
Montgomery has, time and time again, offered to provide proof of his claims made to news outlets on a number of different occasions, including Fox News, who videotaped Montgomery for days recording his claims and law enforcement, but Montgomery failed to produce a single shred of specific information proving his claim as promised. And in his most recent 2016 court case, where Montgomery stood to gain millions in damages in a suit he brought forward, Montgomery astonishingly claimed to a federal judge that he turned over critical software to the FBI and for that reason was no longer in possession of it. While in an all-out effort to remove the burden on himself to prove his claims by producing the software, he redirected the responsibility onto the FBI. Montgomery petitioned the FBI and other agencies to locate the software purportedly contained in the 47 hard drives he had turned over to them under immunity. When it was all said and done, the government could not locate the software and Montgomery finally had to come clean and admit in court he never had it. Again, Montgomery is unable to provide the linchpin evidence that would substantiate all his claims and make him credible, even though he repeatedly makes representations that he is in possession of the evidence.

More notable is the glaring fact that the government was well aware of Montgomery’s 2016 court case and was even asked to assist; however, the government did not intervene in that case with any invocation of the State Secrets Privilege or protective order issued against Montgomery. This after they have received and reviewed all his information under his 2015 immunity agreement, as he claims. Stop and think about that fact. The government felt no compulsion to protect any information Montgomery might reveal in open court after they got it all. That speaks volumes and certainly does not help Montgomery’s claims or his cause.
“The Government has not attempted to intervene in this case, despite the fact that it is well aware of the ongoing dispute over the software. Moreover, the CIA’s response to Defendants’ Touhy requests indicated that they did affirmatively search for a copy of Montgomery’s software and represented that they were unable to locate it. The CIA explicitly did not decline to conduct a search at all on the ground that the material was likely to be classified, as the agency did with respect to the other documents requested.” — Contreras opinion, p. 34
Montgomery has demonstrated behavior throughout his lengthy tumultuous legal history, and most recently with the Sheriff’s Office, that displays an astounding pattern of deception, double-talk, circular fabrications and fraud. Simple logic dictates that if Montgomery did not have the software in 2016, even though he claimed he turned it over to the FBI, and the CIA searched for it but was unable to find it in 2016, and the fact he ultimately admitted in federal court he never actually had it, reason stands that he certainly did not have it in 2013 when he represented to the Sheriff’s Office that he did. In addition it is clear that the CIA in 2016 did search his 47 hard drives. They were not moved to intervene with any form of Protective Order that would indicate his represented privileged information supplied to the FBI had any merit in either 2015 or 2016. The omission of any protective action does not bode well for Montgomery’s claims of Top Secret information contained in his 600 million records classifications. The CIA, DOJ and FBI were not concerned.
All of this was easily discoverable had Fanning and Jones bothered to look. It is clear they didn’t, and it is crystal clear that they are so heavily invested in this narrative that they need it to be true and want it to be true at all costs, so much that they are willing to whitewash him and mitigate his less-than-credible actions through omission of facts and truth. Fanning and Jones, for their own personal agendas, some of which are simply self-serving, are all too willing to defame innocent people who in official capacities have firsthand knowledge and intense interactions with Montgomery. Despite overwhelming evidence contrary to their contrived storyline, they have become traffickers of smear and deception.
Fanning and Jones are two feckless reporters who have self-described as “investigative journalists” focusing on “national security issues.” This should give everyone pause. Their lack of due diligence, flagrant disregard of the facts, outright contempt for the truth they willingly misrepresent, slander and engage in unabashed advocacy for Montgomery at a level that should be alarming to all concerned, especially with the plethora of public information available. They have perpetuated a breathtaking disservice to the listening public and have misled many, including the host of an online talk show.
With all of this being said, Dennis Montgomery did provide some form of information that was verified. Although its origin has never been traced, his historical timeline does put him in contact with state actors who are in the news today. Even though he frauded the Sheriff’s Office, his claim, or at least his historical timeline, needs to be investigated.


“Although former CIA Director John Brennan has been connected to the use of the technology in 2009, he was not then serving in that capacity.”
Is there any independent evidence that Montgomery worked for the government after his Air Force contract was ended in 2009?